Outdated PHP and Joomla!
Friday, September 13th, 2019 - General
It looks like a recent Joomla! update has enhanced the attention of the version of PHP that you are running the Joomla! script on.
It would appear that Joomla! is using a bit of a scare-tactic to try and scare people into believing their PHP version is out of date.
Joomla! will flag PHP 7.1 as out-of-date. This is not the case. As you can see in the link:
https://www.php.net/supported-versions.php
PHP 7.1 is still in-life and is still technically good until November 30, 2019. While it is true that PHP 7.1 is approaching end-of-life… approaching and being are two different things. I’m not sure if the Joomla! developers are aware of the differences between these two words.
We do have plans to update all accounts to PHP 7.3 before the end of November. And we can switch your account to PHP 7.3 now if you would prefer that. But just because Joomla! is telling you that PHP 7.1 is out of date – that is not correct.
Depending on what plugins and components you are using, you may run into compatibility issues with those plugins/components if you update to PHP 7.3. If those plugins/components have not been vetted against PHP 7.3 then they may not work properly. Again PHP 7.1 is approaching end-of-life, so the developers of those plugins and components really need to be working on making their plugins/components compatible with PHP 7.3 – technically right now they are fine if they only operate on PHP 7.1 (after November 30th, 2019 this will no longer be fine).
If you want your account switched to PHP 7.3 now, simply open a support ticket – http://www.amshelp.com/support – and we will be happy to switch your account to PHP 7.3.
•
PHP 7.2 / 7.3 available
Wednesday, April 17th, 2019 - General
We now have PHP 7.2 and PHP 7.3 available on our servers. If you wish to switch to one of these versions on your account, simply open a support ticket – http://www.amshelp.com/support and we will update your account to the desired PHP version.
Please note, there were a lot of changes made in these updates from PHP 7.1. So before updating your account to one of these version, make sure the script you are using is compatible with the desired PHP version.
There is currently (as of April 17, 2019) no need to update your account to one of these PHP versions. These versions are simple being made available for our users that wish to update, for whatever reason. If you have no reason to update to PHP 7.2 or PHP 7.3, then I would not recommend doing so at this time.
The current end-of-life schedule for PHP shows PHP 7.1 (all of our accounts are currently using PHP 7.1) going end of life just before the end of this year – December 1, 2019 (source – https://www.php.net/supported-versions.php)
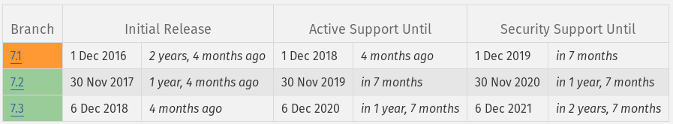
Right now we don’t have a schedule really set in stone regarding our full deployment of these updated PHP versions and the removal of PHP 7.1. We’re probably looking at a schedule that will see us push out PHP 7.3 as the default PHP version on all accounts around late 3Q or early 4Q 2019 (September/October 2019) and then with the removal of PHP 7.1 sometime in December 2019 or early 2020. But that schedule is very fluid right now. Adoption rates of PHP 7.3 are very small right now. That will need to increase before we can feel comfortable pushing PHP 7.3 out. Right now that would be our preference, to skip PHP 7.2 as a default version and go straight to PHP 7.3 – but again the situation is fluid and we are still several months away from having to make any decisions on this.
•
Password Security and Spamming
Monday, October 29th, 2018 - General
Over the weekend we saw a rash of compromised emails accounts that were in turn used to send out spam.
When we investigated these, we found almost all of them using extremely weak passwords and a large majority of those were using passwords that followed the syntax:
Please don’t use passwords like this.
You may think that it doesn’t really matter, but if you’ve ever used your email address any where – then that email address is known. And if you are using a password that follows this syntax or any other easy to guess password structure, it’s trivial for spammers to guess your password and then abuse your account to send out spam.
When your domain name is associated with sending out spam, it starts to build a bad reputation and can start to hurt the deliverability of your legitimate mail. We try to catch these spam events as best we can, but the best course of action is for end users to practice solid password security.
To check the strength of your passwords we recommend:
We have previously posted about the importance of password security at:
The Importance of Password Security
My account was caught sending out spam
•
Bitcoin Ransom Messages
Monday, October 22nd, 2018 - General
Since we seem to getting a lot of messages from our users inquiring about this, we thought it might be a good idea to address this here.
Lately there has been an increase in the number of ransom messages going out threatening to expose certain details about you if you don’t pay the hacker in bitcoin. We really can’t tell you if the message being sent to you and pertaining to you is legit. I don’t think it’s wise for any hosting company or security firm to state as much. But we can advise you on what we are seeing in regards to this. We are seeing a lot of messages like this, so it is very likely a scam in your case, but in the end you will have to make the determination on your own.
The message in question may look something like:

The wording might be a little different. But the same general message is the same. A few key takeaways here:
• This is your password – Is that really your password? Or has it ever been your password? If not, then you can stop right here, it’s a scam! If it is your password, then is it an easy to guess password? Have you reused that password some where else? How do they do this? Pretty simple actually, they pick a random password – usually a pretty common one – and then send out this message to millions and millions of email addresses… it’s bound to be the correct password for a handful of those users. The scam is not meant to work for every single user they email, but if it works for just a handful of users, the scammers make money.
• I sent you an email from your account – This is trivial to do. Email does not have a mechanism in place to verify that the person behind the computer/device that sends a message is actually who they say they are. Mechanisms do exist that can help verify a message was sent from a likely reliable sender, that are done on the recipient end of the message exchange. But those mechanisms aren’t infallible and aren’t universally accepted. How do they do this? Any knowledgeable or trained computer person can send a message to appear to have come from your email address. Just because the From line in an email has your email address does not mean it was sent by your computer or device.
• I made screenshot with using my program from your camera of yours device – Do you computers and devices have cameras on them? Have you actually visited any of the adult rated websites the message suggests? If you answer no to either of these, then it’s a scam! This is a scare tactic aimed to scare individuals into giving the scammers money. The tactic here is that a significant portion of Internet users may visit sites like this. Again, the scammers aren’t expecting the scam to work on 100% of the people they send this message to. It just has to work for a select few and the scammers make money.
• After receiving the specified amount, all your data will be immediately destroyed automatically – Since they have presumably sent this message out to hundreds if not millions of email addresses, how do they know which user a specific payment is referring? So how would they know to discard the information they collected if you pay? Simply answer: They don’t – because 1) they have no information and it’s a scam or 2) they will keep the information and continue to extort you for more money. Again this taps into people’s fears and resolution centers, that money can fix all problems and that’s what the scammers are hoping for.
• What information is missing? – If the scammers really wanted you to believe their message and if they had really stolen some of your information, don’t you think they would have addressed you by name? Or at least given some proof that they have. In kidnapping/ransom cases negotiators will ask for “proof of life” or proof that the kidnappers have the person in question, negotiators want this assurance before giving any ransom. In this particular case all the scammer has is a password that might not even be yours and if it is – it’s a common password that many people use and a scare tactic that they sent the email from your very own email address which is trivial for any knowledgeable computer person to do.
So is the message a scam? Probably. But this is something you really need to make a determination for yourself. I can tell you that we are seeing many complaints about such messages and we’re even getting them as well. So if you think you are being singled out and are the only one receiving these messages, know that you are not.
How can you protect yourself?
• Keep an up-to-date virus and malware detection system. A malware detection system like MalwareBytes can be helpful in regards to this.
• Keep your computer up to date. When computer vulnerabilities are discovered, programmers and developers that wrote that software will work to fix the security holes that led to that vulnerability. But it does you absolutely no good if you never install the updated code that they developed. If you want your computer and device to be safe and secure you have to apply security updates as soon as they become available.
• Use strong and secure passwords. If you are using simple and easy to guess passwords then this just increases the chances of your password being compromised. It may be difficult to remember a strong and secure password, but it’s going to be even more difficult when your password is compromised and your information is leaked out.
• Don’t reuse your passwords. If you’re using the same password for everything, then all it takes is for one service to suffer an information leak, and then the password you are using for everything is then in the public domain and capable of being compromised. Use separate, strong, and secure passwords for every service you use.
• Keep a backup of your files. If the files on your computer and device are important to you, make sure you keep a copy of them stored some where off of the computer or device. This way if you ever do get compromised or have your files deleted, you will have something to restore from.
Again, our aim is to give you the tools and information so that you can make your own informed decisions. If you are relying on someone else to make this determination for you, then you can fall victim if their determination is wrong. Educating yourself is the best defense you can have in regards to scams like this.
•
Upcoming PHP 5.6 disabling
Monday, October 15th, 2018 - General
(Update: October 16 – This will also apply to users using PHP 7.0, but there are very, very few users using PHP 7.0. We skipped PHP 7.0 as a default version and went straight to PHP 7.1 so there are only a handful of PHP 7.0 users that will be affected by this)
We will be switching accounts that use PHP 5.6 to PHP 7.1 on November 20, 2018. This date is more than a month away, if you are affected by this, please use this time to work towards updating your script/web application/plugins to be PHP 7.1 compatible.
Why is it important to switch to remove PHP 5.6?
PHP 5.6 is approaching end-of-life. If you don’t believe me, you can visit the php.net website and see the full schedule:
http://php.net/supported-versions.php
There you can see PHP 5.6 will receive security support updates until December 31, 2018 – that is fastly approaching. We did not design this schedule. This is simply PHP’s schedule of life for it’s programming language. It is not a good idea to rely on a programming language that is not being supported by it’s developers.
My script works, why do I have to upgrade it?
Just because your script works, doesn’t mean it’s not being exploited or has security holes that cannot be compromised. A lot of hacks and abuse happen because hackers are able to burrow their way into a website’s script or web application and perform malicious actions without the website owner knowing about it. If you are using a script, web application, or plugins that still relies on PHP 5.6 then chances are great that the developer of that script/web application/plugin has not audited the security of their work in several years.
If your account is using a script, web application, or plugin that still requires PHP 5.6, then it falls into 1 of 2 categories:
• The script, web application, or plugins you are using are out of date. Updates may be available but for whatever reason, you have not applied them to your account. Updates have to be applied to your account in order for you to reap the benefits of those updates. I think sometimes people may think that just because an update to a script/web application/plugin is released to the public then they are protected. That is not the case. Developers release updates of their products, but it’s up to the users of those products to grab the updates and apply them to their account.
• The script, web application, or plugin you are using has been abandoned by it’s developers. This is called abandonware and it is quite common. A developer may create a script, web application, or plugin release it to the public – they may even release a few updates for it – but eventually it becomes too time consuming for the developer and they quit publishing updates or working on the project and the project becomes abandoned. This puts the people that have installed and used that particular script, web application, or plugin in a difficult spot. This is why we always encourage you to use only reputable scripts, web applications, and plugins – items that have a higher confidence of staying actively developed.
Developers of scripts, web applications, and plugins have a responsibility to stay in tune with the current scheduling of the programming language they are using. There’s really no excuse for a reputable developer to be unaware of PHP 5.6 upcoming end-of-life at the end of 2018. I know that I would not want to put a lot of trust in a developer that is caught off guard of this upcoming end-of-life.
So what actually is going to happen on November 20, 2018?
On Tuesday November 20th, 2018 we will begin switching accounts that are using PHP 5.6 to PHP 7.1. If you find your website to no longer be working after this switch, contact us and let us know and we will reluctantly switch your account back to PHP 5.6. But please understand, you are going to have to get with it, because PHP 5.6 will be removed at the end of 2018 meaning a downgrade to PHP 5.6 will no longer be possible.
Why are you pushing PHP 5.6 out the door?
Because we believe in a safe and secure Internet. We believe scripts that still rely on PHP 5.6 are a security risk to you, to our servers, and to the rest of the Internet users. Compromised scripts, web applications, and plugins is what leads to spamming, phishing attacks, information leaks, and other malicious/abusive actions. Our purpose in all of this is to promote a safer and secure hosting environment for all of our users.
When will PHP 5.6 be completely disabled?
Our hope is that by November 20, 2018 everyone that was using PHP 5.6 will have updated their scripts/web applications/plugins to PHP 7.1 compatible versions. But we will reevaluate where we stand after November 20, 2018. We may have to do another round of disabling PHP 5.6 in December depending on what the uptake is for this November 20th deadline.
My script requires PHP 5.6 and there is no update to it.
See the abandonware paragraph above. If your script requires PHP 5.6 and there is no update for it, then it has been abandoned by it’s developers and you need to seek an alternative script/web application/plugin.
Can you please give me more time to get ready for this November 20th deadline?
No, unfortunately we cannot push this date back any further. If you are still having issues with this on November 20th after your account has been switched to PHP 7.1, contact us and we will reluctantly switch you back to PHP 5.6. But please understand you are getting very close to the deadline for PHP 5.6 to officially become end-of-life. We are not going to push back this November 20th soft deadline because it will take away the sense of urgency to this matter.
Can you use a hardened version of PHP 5.6?
No, this is not something we philosophically believe it. The issue at hand isn’t really so much the PHP version, the issue is more the fact that you are using a script that requires an end-of-life version of PHP. Hardening old versions of PHP is fine, but it’s not going to stop compromises and security holes in old scripts/web applications/plugins that rely on these end-of-life versions of PHP. And a hardened PHP version is not going to protect your outdated, security-hole filled script from being exploited.
